Learn how to add HTTPS encryption to your Spring Boot application running inside a Docker container.
Since the arrival of free Let’s Encrypt certificates, there is really no excuse not to use HTTPS for encrypting your application traffic.
Obtaining and integrating a free HTTPS certificate is easy and only requires three simple steps. This article shows the integration for a CentOS 8 web server with a Dockerized Spring Boot application.
Registering a Certificate
On your web server, obtain certbot, the official registration tool from Let’s Encrypt:
git clone https://github.com/certbot/certbot cd certbot
Create a certificate using a standalone web server for the HTTP challenge (replace your domain name accordingly – also make sure your port 80 is currently free):
./certbot-auto certonly -a standalone -d example.com -d www.example.com
Change to the created directory and convert the obtained files to the PKCS12 format which is needed for Spring Boot:
cd /etc/letsencrypt/live/example.com openssl pkcs12 -export -in fullchain.pem -inkey privkey.pem -out keystore.p12 -name tomcat -CAfile chain.pem -caname root
Adding the Certificate to your Docker Image
Depending on how you build your Docker image, you need to somehow add the generated certificate file to your image. In my case, I simply add an “ADD” statement to the Dockerfile:
ADD keystore.p12 /etc/letsencrypt/live/www.example.com/keystore.p12
Make sure that you copy the generated p12 file to the same folder where the Dockerfile is located because the “ADD” command expects a relative path as a first argument.
Adapting your application.properties
Either directly append these lines to your application.properties or add the corresponding keys as environment variables as described in this article (the keys need to be transformed to underscore-separated capitalised letters – e.g., SERVER_SSL_KEYSTORE="..."):
server.ssl.key-store:/etc/letsencrypt/live/www.example.com/keystore.p12 server.ssl.key-store-password: server.ssl.keyStoreType: PKCS12 server.ssl.keyAlias: tomcat
Certificate Renewals
You need to renew your Let’s Encrypt certificate regularly. Use the certbot tool with the following parameters:
certbot-auto certonly -a standalone -d subdomain.example.org
and copy the resulting certificate to the same location used before. Then restart your Docker container and you are done – your certificate has been renewed.
Also make sure your port 80 is still free – if you have an application running on that port, stop it for a few seconds (you can restart it immediately after the invocation of certbot-auto) – otherwise the renewal process might fail.
Conclusion
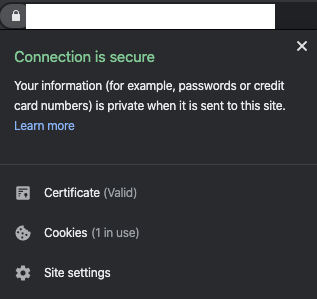
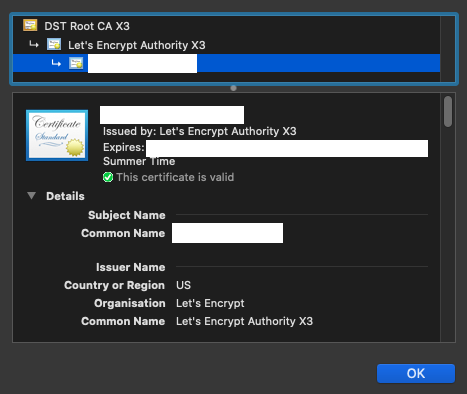
You can verify whether the certificate works by running your application and targeting your browser to its URL with the https:// prefix – you should see the following HTTPS information:
A Tons of thanks to the Author , it helped to resolve my long pending issue , Just add one comment if anyone putting certificate and its not working doc heck your port 443 much be accessible (i faced this issue on VPS)